Identifying Threats using Gigamon Precryption™ in Container based Environments (6.4)
Introduction
Nearly 90% of all internet traffic is encrypted and enterprises use encryption to protect communication data. The TLS cryptographic protocol is used to secure an ever-increasing portion of the internet’s web, messaging, and application data traffic. The TLS protocol is leveraged by the secure HTTP (HTTPS) web protocol, StartTLS email protocol, Tor anonymizing network, and virtual private networks, such as those based on the Open VPN protocol as well as to encapsulate their contents—protecting them from being observed or modified in transit. While encryption ensures privacy and confidentiality, it creates a serious blind spot for security.
For example, when you download a document from an external website, your firewall or intrusion detection system can inspect the data packets coming through the local network. But if the same communication happens over an SSL connection, then the system cannot see through the encryption to detect what is really inside the document. This provides a way for attackers to bypass inspection by taking advantage of encryption. It also prevents defenders from detecting or stopping deployment of malware. The attackers deliver malware inside the network and remove or steal the data without getting exposed.
To overcome this, Gigamon has introduced the exemplar feature "Precryption™" to acquire the traffic before encryption or after decryption in the monitored VM's or Containers. Using this approach, the tool can easily identify whether it is an in-house generated traffic like HTTPS, Secured SMTP, and son on or malware generated traffic. This feature also eliminates the requirement of keys in security tools to decrypt the traffic thus removing the blind spots in all encrypted cloud traffic.
As packets synthesized by Precryption™ carry sensitive data, there is a need to deliver these packets in a secure manner for further processing. Gigamon addresses this requirement by sending the precrypted data through secure tunnels. The secure tunnels can also be used to securely transport packets tapped by any other means.
In this GVD, we explain the deployment of Gigamon Precryption™ solution for obtaining the precrypted traffic in the Container-based setup in Azure AKS and forward it securely to the V-Series node using a secure tunnel in Azure cloud.
Refer to Gigamon Validated Designs in the Gigamon community's knowledge base for more such designs. Please contact your Gigamon Sales contact for more information about the Gigamon solutions.
Design Overview
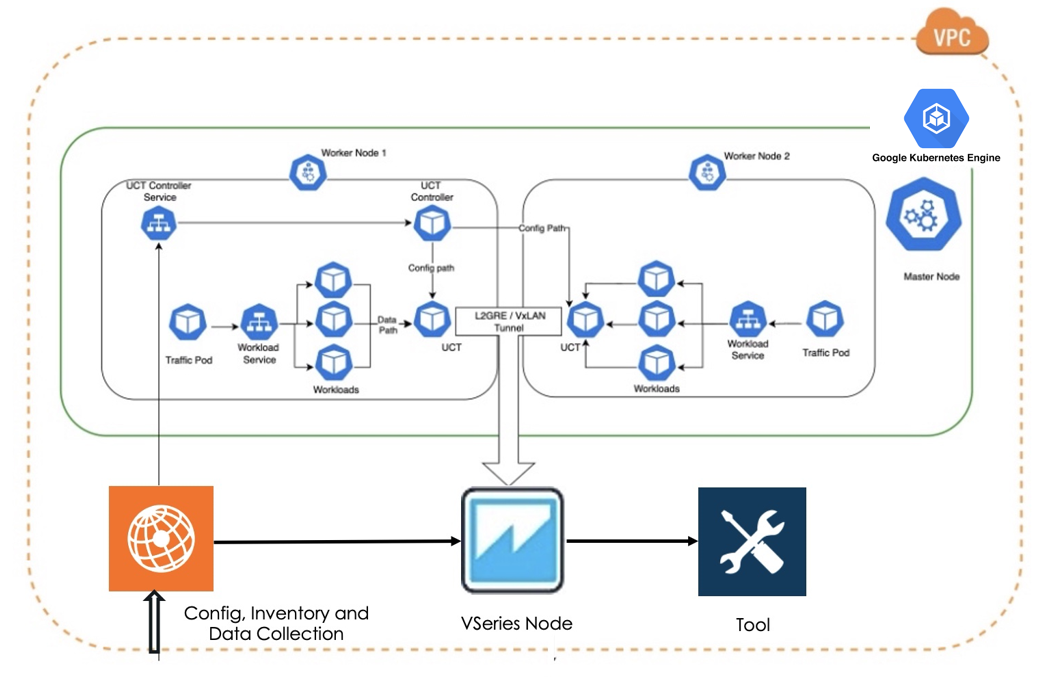
This design illustrates deploying Gigamon Cloud Suite in Azure AKS. In the AKS cloud, traffic from the clusters will be acquired using kernel hook and forwarded to the V-Series nodes for traffic aggregation. The V-Series node will aggregate and process the acquired traffic using GigaSMART (GS) applications and subsequently, forward it to tools.
The following components of Gigamon Cloud Suite will be deployed in this solution:
-
GigaVUE-FM: A web-based fabric management and orchestration interface that provides a single-pane-of-glass visibility of both physical and virtual traffic in the UCT-C.
-
UCT-C Controller: The management component of UCT-C to control and communicate with UCT-C pods. The UCT-C controller collects the data from the UCT-C pods and sends the collected statistics and heartbeats to the GigaVUE-FM.
-
UCT-C Pod: The primary UCT-C module responsible for programming eBPF configurations, such as tapping containers, traffic to be filtered, adding tunnel encapsulation to the filtered traffic, and forwarding to the tools or to GigaVUE V Series 2.0 nodes. The UCT-C Pod also sends the statistics and heartbeats to UCT-C Controller.
-
GigaVUE V Series node: For aggregating all the traffic, optimizing the traffic by removing the duplicate packets, and forwarding the traffic to either new or existing tool probes.
To learn more about this solution, read complete details on the Gigamon Community: Identifying-Threats-using-Gigamon-Precryption-in-Container-based-Environments-6-4