Sanitizing Monitored Traffic to Improve Tools' Performance (6.0)
Introduction
Enterprise networks can be complex owing to increased network and server virtualization. In such scenarios, the security and monitoring tools need to be competent to have complete visibility of the north-south and east-west traffic. Note that the traffic could traverse underlay and overlay network, such as VXLAN, L2GRE or Geneve creating duplicate streams of data. This can pose significant challenge to the existing security tools stack. These challenges include:
- The tools may not support parsing one/more overlay traffic
- The tools could be oversubscribed and exacerbate the licensing requirement for deploying new tools, such as Security Information and Event Management (SIEM) tool.
These operational challenges can be mitigated by deploying Gigamon Hawk or Gigamon hybrid cloud visibility and analytics solution. These solutions help in acquiring and optimizing the network traffic before forwarding to the tools. This Gigamon Validated Design (GVD) illustrates one such scenario.
Topology Diagram
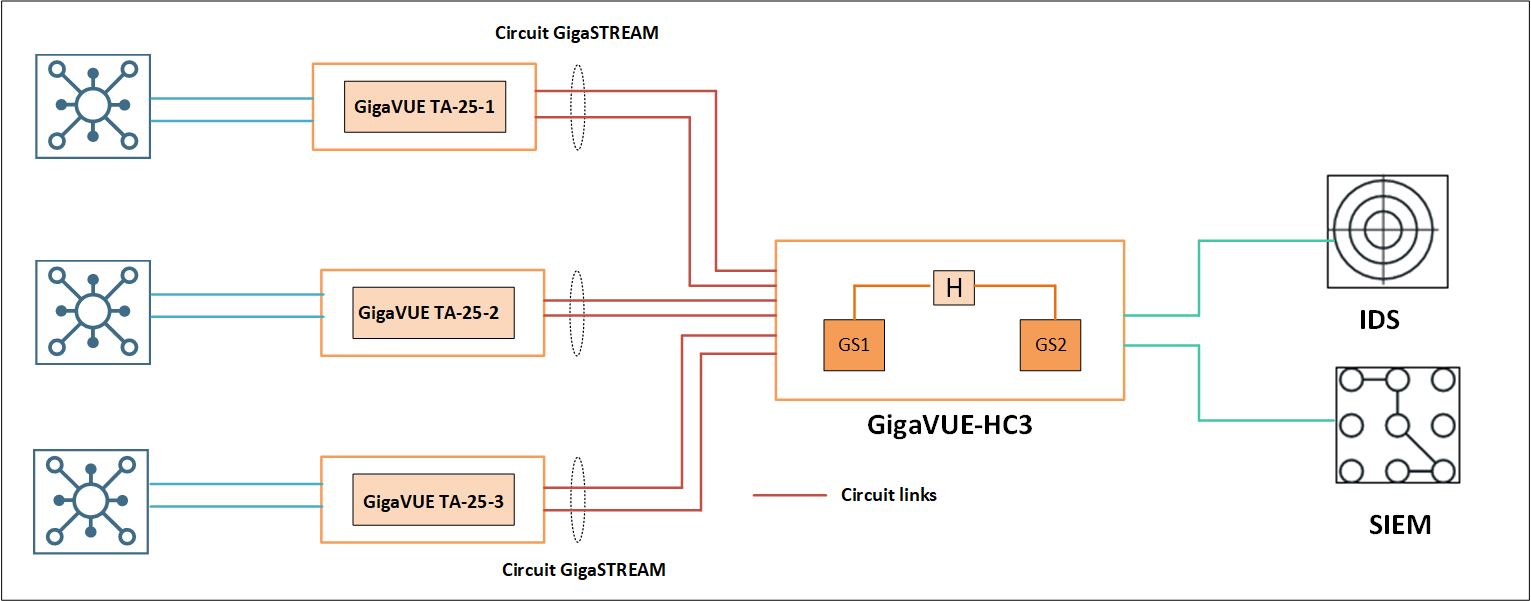
Design Overview
This design presumes an enterprise network tapping traffic from myriad sources (physical/virtual/cloud). The tapped traffic can be aggregated using traffic aggregators, such as GigaVUE TA-25, which supports 1G, 10G, 25G, and 40G interface types. Traffic from the traffic aggregators will be centrally processed using Gigamon H series nodes, such as GigaVUE-HC3 to achieve the following:
- Strip the overlay headers. For example, VXLAN, L2GRE, ERSPAN
- Remove the duplicate packets.
- Forward relevant L2-L7 traffic to the existing tools, such as IDS.
- Export L2-L7 metadata (CEF/IPFIX) to SIEM. For example, extracting the attributes from the protocols, such as HTTP/S and, DNS.
The volume of traffic to be monitored would determine the required GigaVUE H Series device and the number of GigaSMART modules.
GigaSMART operations can be deployed separately or combined with the other Gigamon visibility solutions. While the first step above (Tunnel Decapsulation) cannot be combined with the other GigaSmart operations (De-duplication, Application Filtering, and Application Metadata). Please contact Gigamon sales representative to seek advise on the options that can meet your needs.
After the first step, ie.e., tunnel decapsulation is completed, the traffic should be looped back to proceed with the next steps. You can either physically loop back the traffic or use a hybrid port (recommended).
The tunnel decapsulation can also be moved to GigaVUE TA-25. Please refer to the GigaVUE-FM user guide and release notes for more details.
To learn more about this solution, read complete details on the Gigamon Community: Sanitizing Monitored Traffic to Improve Tools' Performance (6.0)