GigaSMART Passive TLS/SSL Decryption
GigaVUE H Series nodes support Secure Sockets Layer (SSL) decryption. TLS/SSL is a cryptographic protocol that adds security to (Transmission Control Protocol) TCP/IP communications such as Web browsing and email. The protocol allows the transmission of secure data between a server and client who both have the keys to decode the transmission and the certificates to verify trust between them. Passive TLS/SSL decryption delivers decrypted traffic to out-of-band tools that can then detect threats entering the network.
Passive TLS/SSL decryption is a pillar of the GigaSECURE Security Delivery Platform. For an overview of GigaSECURE, refer to GigaSECURE Security Delivery Platform.
On GigaVUE H Series nodes, GigaSMART line cards or modules perform the decryption of TLS/SSL traffic. Using GigaSMART for decryption offloads the decryption function from tools and offers improved tool performance by removing this computationally intensive task. GigaSMART provides a centralized decryption point. Decrypted TLS/SSL traffic can be sent from GigaSMART to inspection tools for further analysis, for example, to look at encrypted communications or to detect malware.
Before TLS/SSL traffic is decrypted, the de-duplication GigaSMART operation can be performed. Decrypted traffic from the GigaSMART line card or module can be filtered, aggregated, and replicated and then sent to one or more monitoring tools for analysis.
Passive TLS/SSL decryption is supported on the following GigaVUE H Series products with GigaSMART line cards or modules installed:
| GigaVUE‑HC3 |
| GigaVUE‑HC1 |
| GigaVUE-HC1-Plus |
| GigaVUE-HCT |
Use Passive TLS/SSL decryption on the GigaSMART line card or module with passive or offline traffic. Tap the traffic to and from a server and pass it to the GigaVUE H Series node with the GigaSMART line card or module.
Passive TLS/SSL decryption operations can be assigned to GigaSMART groups consisting of multiple engine ports. Refer to Groups of GigaSMART Engine Ports for details.
For secure storage of private keys, Entrust nShield Hardware Security Module (HSM) is integrated with Passive TLS/SSL decryption. Refer to Entrust nShield HSM for TLS/SSL Decryption for Out-of-Band Tools for details.
Gigamon also offers inline TLS/SSL decryption, which inspects TLS/SSL encrypted traffic inline. Refer to Inline TLS/SSL Decryption for details.
TLS/SSL encryption secures traffic between a client and a server, such as a Web server. TLS/SSL decryption uses keys to decode the traffic between the client and server.
SSL and Transport Layer Security (TLS) protocols consist of a set of messages exchanged between a client and server to set up and tear down the TLS/SSL connection between them. To set up the connection, the client and server use the Public Key Infrastructure (PKI) to exchange the bulk encryption keys needed for data transfer.
1 shows the basic TLS/SSL handshake between a client and server to establish a session. The messages are unencrypted up to step 6 in 1. The messages are encrypted after step 6, including the step 9 Finished message.
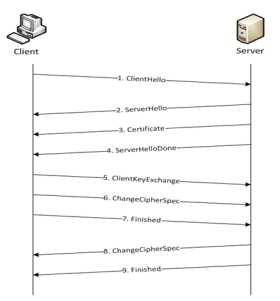
| 1 | Basic TLS/SSL Handshake |
Once a session has been established, the keys are saved so a session can be resumed efficiently later. 2 shows the resumed TLS/SSL handshake, with fewer steps.
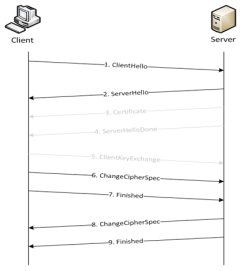
| 2 | Resumed TLS/SSL Handshake |
Passive TLS/SSL decryption can be deployed close to the server, as shown in 3.
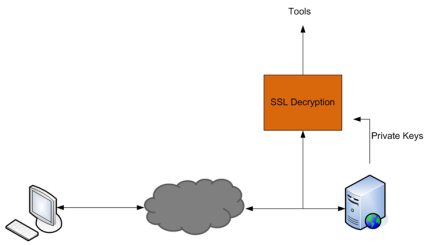
| 3 | Inbound (Server Side) |
Passive TLS/SSL decryption can also be deployed close to an TLS/SSL proxy, with the server in the Enterprise domain as shown in 4.
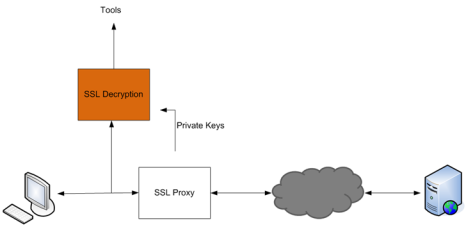
| 4 | Outbound (Client/Enterprise Side) |
In 3, tap traffic to the server and then send it for decryption. In 4, tap traffic to the proxy and then send it for decryption. You can have a deployment with either a server or a proxy, but not both.
The supported protocols are as follows:
| SSL 3.0 |
| TLS 1.0 |
| TLS 1.1 |
| TLS 1.2 |
The supported authentication (Au) is as follows:
| RSA |
The supported key exchange (Kx) is as follows:
| RSA |
The supported encryption algorithms (Enc) are as follows:
| NULL |
| RC4 |
| DES |
| 3DES |
| AES (including GCM mode) |
| CAMELLIA |
| SEED |
| IDEA |
The supported compression algorithm is as follows:
| NULL |
The supported digest algorithms are as follows:
| MD5 |
| SHA1 |
| SHA2 |
The supported key sizes are 128, 256, 512, 1024, 2048, and 4096.
The supported TLS extensions are as follows:
| Extended Master Secret, RFC 7627 |
| Encrypt-then-MAC, RFC 7366 |
The supported ciphers are listed in Table 5: Supported Ciphers for Passive SSL decryption.
|
Cipher Name |
Kx |
Au |
Enc |
Bits |
Mac |
|
TLS_RSA_WITH_NULL_MD5 |
RSA |
RSA |
NULL |
0 |
MD5 |
|
TLS_RSA_WITH_NULL_SHA |
RSA |
RSA |
NULL |
0 |
SHA |
|
TLS_RSA_EXPORT_WITH_RC4_40_MD5 |
RSA_EXPORT |
RSA_EXPORT |
RC4_40 |
40 |
MD5 |
|
TLS_RSA_WITH_RC4_128_MD5 |
RSA |
RSA |
RC4_128 |
128 |
MD5 |
|
TLS_RSA_WITH_RC4_128_SHA |
RSA |
RSA |
RC4_128 |
128 |
SHA |
|
TLS_RSA_EXPORT_WITH_RC2_CBC_40_MD5 |
RSA_EXPORT |
RSA_EXPORT |
RC2_CBC_40 |
40 |
MD5 |
|
TLS_RSA_WITH_IDEA_CBC_SHA |
RSA |
RSA |
IDEA_CBC |
128 |
SHA |
|
TLS_RSA_EXPORT_WITH_DES40_CBC_SHA |
RSA_EXPORT |
RSA_EXPORT |
DES40_CBC |
40 |
SHA |
|
TLS_RSA_WITH_DES_CBC_SHA |
RSA |
RSA |
DES_CBC |
56 |
SHA |
|
TLS_RSA_WITH_3DES_EDE_CBC_SHA |
RSA |
RSA |
3DES_EDE_CBC |
168 |
SHA |
|
TLS_RSA_WITH_AES_128_CBC_SHA |
RSA |
RSA |
AES_128_CBC |
128 |
SHA |
|
TLS_RSA_WITH_AES_256_CBC_SHA |
RSA |
RSA |
AES_256_CBC |
256 |
SHA |
|
TLS_RSA_WITH_CAMELLIA_128_CBC_SHA |
RSA |
RSA |
CAMELLIA_128_CBC |
128 |
SHA |
|
TLS_RSA_WITH_CAMELLIA_256_CBC_SHA |
RSA |
RSA |
CAMELLIA_256_CBC |
256 |
SHA |
|
TLS_RSA_WITH_SEED_CBC_SHA |
RSA |
RSA |
SEED_CBC |
128 |
SHA |
|
TLS_RSA_WITH_NULL_SHA256 |
RSA |
RSA |
NULL |
0 |
SHA256 |
|
TLS_RSA_WITH_AES_128_CBC_SHA256 |
RSA |
RSA |
AES_128_CBC |
128 |
SHA256 |
|
TLS_RSA_WITH_AES_256_CBC_SHA256 |
RSA |
RSA |
AES_256_CBC |
256 |
SHA256 |
|
TLS_RSA_WITH_AES_128_GCM_SHA256 |
RSA |
RSA |
AES_128_GCM |
128 |
SHA256 |
|
TLS_RSA_WITH_AES_256_GCM_SHA384 |
RSA |
RSA |
AES_256_GCM |
256 |
SHA384 |
All algorithms used for Passive TLS/SSL decryption are FIPS 140-2 compliant.
All key URLs must point to an RSA private key stored in the PEM or PKCS12 format, as follows:
| http://keyserver.domain.com/path/keyfile.pem |
| https://keyserver.domain.com/path/keyfile.pem |
| ftp://keyserver.domain.com/path/keyfile.pem |
| tftp://keyserver.domain.com/path/keyfile.pem |
| scp://username[:password]@keyserver.domain.com/path/keyfile.pem |
The supported applications are as follows:
| HTTPS |
| FTPS |
| SMTP, IMAP, and POP3 with StartTLS |
The limitations of Passive TLS/SSL decryption are as follows:
| Only IPv4 |
| Only regular maps; no virtual ports (vports) |
| Only combined with the de-duplication GigaSMART operation |
| Only one private key per PKCS12 file |
| Only server-side authentication |
| Only the protocols and ciphers listed in Supported Protocols, Algorithms, and CiphersS. |
Note: If an TLS/SSL session cannot be decrypted due to having a non-supported protocol or cipher and if the GS Parameter SSL Decryption has Decrypt Fail Action is set to Pass to Tool Port, the packets will be forwarded to the tool without decryption . Non-supported ciphers and protocols include SSL 2.0, Diffie-Hellman (DHE keys), Ephemeral keys, Elliptic Curves Extension, compression, and 8K key size.
The GigaSMART license for Passive TLS/SSL decryption is installed as any other license.
There are no limits to the number of Passive TLS/SSL decryption sessions or the number of users.
To perform the configuration in the following section, you must have an admin level access role.
Before uploading keys or configuring TLS/SSL, you must create an SSL keychain password. The password is used to encrypt the private keys that you upload to the node.
Keychain passwords are not saved on the node. Refer to Notes about Private Keys and Passwords.
Note: When uploading TLS/SSL keys, make sure that you are not creating a duplicate key. Adding a duplicate key can cause errors.
To create an TLS/SSL keychain password, use the following steps:
-
On the left navigation pane, click
 , and then select Physical > Nodes.
, and then select Physical > Nodes. -
In the Physical Nodes page, select the node for which you want to create the Key Store password.
-
Go to GigaSMART>Passive SSL >Key Store.
-
Click Keychain Password.
-
Enter a password in the Password and Confirm Password fields.
You can only configure a strong password. A strong password should include at least eight (8) or more characters (up to 64) and include the following:
one uppercase letter one lowercase letter one numerical character one special character -
Enable the Auto login check box to let GigaVUE-FM unlock the key store when the node reboots.
-
Click Submit.
After keys are installed on the node, you will be prompted to enter the password after any login as well as after a node reboot, for example:
If you are a user who does not have an admin level access role, when you enter the configure terminal mode, the following message is displayed:
Password required. Please contact administrator.
If you are a user with an admin level access role, but you enter an incorrect password, the following message is displayed:
Password does not match. Please reenter the password
If an TLS/SSL keychain password is lost, it can be reset, but all existing private keys will be revoked. When there are keys installed on the node, a warning is displayed before you are prompted for the new password.
Once you have a new password, you will have to upload the keys again.
This section describes working with private keys as well as services. Keys must be uploaded to the GigaVUE H Series node using a unique alias. Services must be defined for each server destination that needs decryption. There are two types of decryption. If the service is associated with a certificate then it is called service based decryption. If only certificate is added to the node without creating service then it is key certificate based decryption.
To perform the configuration in the following section, you must have an admin level access role.
Encrypted private keys are saved on the node. Refer to Notes about Private Keys and Passwords.
Note: When uploading TLS/SSL keys, make sure that you are not creating a duplicate key. Adding a duplicate key can cause errors.
A Key Store certificate can be setup to be auto- enabled, auto-deleted and auto-retained to a passive TLS/SSL service. The configuration can be done as follows:
-
On the left navigation pane, click
 , and then select Physical > Nodes.
, and then select Physical > Nodes. -
In the Physical Nodes page, select the node for which you want to configure Key Store settings.
-
Go to GigaSMART>Passive SSL >Key Store.
-
Click Settings. Configure the following settings:
| Auto Enable New Certificates – This setting is not applicable for passive TLS/SSL service. |
| Auto Delete Expired Certificates – This option allows you to delete the expired certificates automatically. This setting will be triggered once a day at 12:00:00 UTC. Specify the number of days to retain an expired certificate in the Number of days to retain expired certificates field. The default value would be 30 days. |
| Auto Delete Certificates with same entity – This option allows you to automatically delete expired certificates that have a similar name and are associated with a passive TLS/SSL service. When you enable this option, you need to specify the maximum number of certificates to retain for the same entity in the corresponding field. This means that if there are more certificates than the specified number, the oldest one will be deleted. This helps you manage your certificates and avoid cluttering your system with unnecessary or redundant certificates. |
To upload an TLS/SSL private key, do the following:
- From the device view, select GigaSMART >Passive SSL > Key Store to open the Key Store page.
- Click New. The SSL Key page appears.
- In the Add Key page, enter the following details:
- For Key Alias, enter an alias for the SSL key.
- For Key Type, select RSA or ECDSA.
- For File Type, select PEM, PKCS12 or PKCS11.
- (optional) For Passphrase, enter a passphrase for the key.
- Select a Private Key by pasting the copied key in PEM format or installing from URL or installing from local directory.
- Select a Certificate by pasting the copied key in PEM format or installing from URL or installing from local directory.
Note:
- You can either use the server based private key or the key certificate based private key to decrypt a passive TLS/SSL traffic.
- If the Entrust nShield HSM for TLS/SSL Decryption for Out-of-Band Tools is enabled in TLS/SSL Service, you cannot use the server certificate to decrypt Passive TLS/SSL traffic.
- Click OK.
If you choose to use Venafi, Inc. as your Electronic Key Management System (EKMS), ensure that you have the GigaVUE‑FM host address and credentials to push the generated key into the selected nodes. For details on pushing keys from Venafi, see the GigaVUE-FM/Venafi Trust Protection Platform Integration Guide.
To delete a particular SSL private key, select the key on the TLS/SSL Keys page, and then select Delete. To delete all TLS/SSL private keys, select multiple keys.
The key store certificates added would be displayed in the Key Store page.
To access the Key Store page:
-
On the left navigation pane, click
 , and then select Physical > Nodes.
, and then select Physical > Nodes. -
Select the node for which you want to view the key store certificate information.
-
From the left navigation pane, go to System > GigaSMART > Passive SSL > Key Store. The details about the key store certificates added for the selected node is displayed.
The following table describes the fields:
|
Component |
Description |
|---|---|
|
Key Alias |
The alias name of the Key certificate. |
|
Type |
Defines whether the Key Store is a Certificate or a Private Key . |
|
Health Status |
The health indicator of a certificate used in traffic flow. The three major indicators with their respective color legend are as follows: Green Blue Red |
|
Common name |
A common name given to group the key based on domain. |
|
Organization |
Organization name that provided the key . |
|
.Organization Unit |
Organization unit name that provided the key. |
|
Expiry Date |
Date on which the key certificate would get expired. |
|
Installed On |
Date on which the key certificate was installed. |
|
Description |
Description or additional information about the key certificate. |
|
Status |
Status of the key certificate. The valid values are: Expiring—The key certificate is nearing the expiry date. Expired—The key certificate has expired. |
You can control the key store certificates display by utilizing the filters provided.
After you have uploaded a private key, you can add a service. A service maps to a physical server, such as an HTTP server. One server can run multiple services. A service is a combination of an IP address and a server port number. Also, the key and the service must be tied together.
Prerequisites
Before creating a service, you must do the following:
| Upload a private key as described in Upload TLS/SSL Private Keys |
| Create GigaSMART Group with TLS/SSL Decryption enabled. |
To create a service, do the following:
| 1. | From the device view, select GigaSMART > Passive SSL > SSL Services. The SSL Services page appears. |
| 2. | Click New. |
| 3. | On the SSL Service configuration page, do the following: |
| Enter an alias. |
| Click on the Default Service (inbuilt key will be used for decryption for any service) check box to allow GigaVUE‑FM to enable default service. |
Note: When opting for the Default service along with service based decryption, other than the particular service that is opted for service based, other connections will be decrypted using the key available on the default service.
| Enter the information for the service: IP Address, Server Port. |
| Select the alias of SSL Key previously uploaded. For the steps, refer to Upload TLS/SSL Private Keys. |
| Select the GigaSMART Group with TLS/SSL decryption enabled to associate with this TLS/SSL service. |
| 4. | Click Apply. |
Delete TLS/SSL Service
To delete a particular TLS/SSL service select the service on the TLS/SSL Services page, and then select Delete. To delete all TLS/SSL services, select multiple keys.
Notes about Private Keys and Passwords
Consider the following notes about private keys and passwords:
| Encrypted private keys are stored on the node. When a private key is uploaded, it is encrypted with a password before it is stored, therefore keys are password-protected. Keychain passwords are not stored on the node. |
| Because only encrypted private keys are stored on the node and because the keychain password is not stored on the node, after any node reboot you will be prompted to enter the password. Until the password is entered, Passive TLS/SSL decryption is not working. |
| Key content cannot be displayed. |
| Keys that are synchronized across a cluster are encrypted. |
Use the following table of ECODE messages to assist with troubleshooting Passive TLS/SSL decryption:
|
ECODE |
Description |
|
81 |
TCP flow errors detected. Make sure you see the complete TCP flow. Use the de-duplication GigaSMART operation with Passive TLS/SSL decryption. |
|
103 |
Session limit reached. The session table has been exhausted. If the session timeout (session-timeout) value is large, lower it. |
|
104 |
Key/ticket cache limit reached. The allocated cache entries have been used up. If the timeout (key-cache-timeout or ticket-cache-timeout) value is large, lower it. |
|
206 |
No server info. A flow has been received for which service-key mapping is not defined. |
|
213 |
Packets for missed TCP handshake. Packets were received for TCP flows that do not exist. If the device was just started, this should trend down quickly. |
|
218 |
Unknown TLS/SSL version. An TLS/SSL handshake processing error occurred. Use the de-duplication GigaSMART operation with Passive TLS/SSL decryption. |
|
221 |
Unknown TLS/SSL version. An unsupported TLS/SSLv2 handshake was seen. |
|
222 |
Protocol error. An unsupported protocol version was seen. |
|
225 |
Unsupported cipher. The cipher suite cannot be decrypted. |
|
226 |
Pre-master secret error. Check that the private key is correct and that the session is complete. |
|
228 |
Generic decryption error. Usually indicates errors in the handshake. Check that you are getting the full session from both sides. |
|
231 |
Invalid MAC. Likely indicates that invalid or truncated packets have been received. |
|
232 |
Session not in cache. Indicates that you are trying to decrypt a restarted session where the original negotiation was not seen. These should trend down in time, but if they do not, increase the key-cache-timeout value. |
|
237 |
Cannot decrypt ephemeral key based encryption. One of the Ephemeral/PFS ciphersuites, usually Diffie-Hellman Ephemeral, has been seen. These are not supported. |
|
245 |
Ticket not in cache. This is usually not an error. Indicates that you are trying to decrypt a restarted session where the original negotiation was not seen. These should trend down in time, but if they do not, increase the ticket-cache-timeout value. |
GigaSMART provides support for Flow Ops reporting. You can generate the Flow Ops report for Passive TLS/SSL Decryption, view the session summary and session statistics, and export the report to a remote server.
To view the session summary and session details of the Passive TLS/SSL Decryption Flow Ops report:
-
From the device view, go to System > GigaSMART > Passive SSL > Session Statistics.
-
From the GigaSMART Group drop-down list, select the required GigaSMART group. The Session Summary and Session Details appear. For descriptions of the session statistics, refer to Flow Ops Report Statistics for Passive TLS/SSL Decryption.
-
In the Session Summary table, click the Report Summary link to view the graphical representation of the trending data for the Passive SSL Decryption session summary as shown in the following figures:
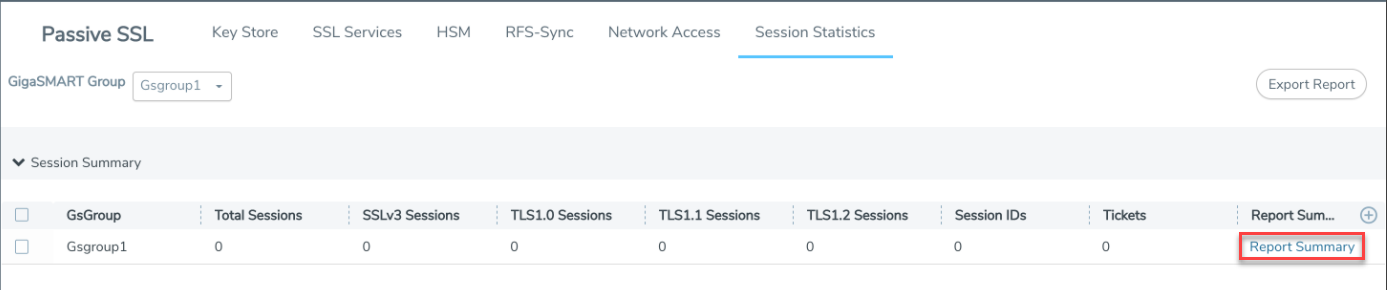

You can also choose to export the session summary to a remote server. Select the required row in the Session Summary table, and then click Export Report. The Upload Flow Ops Report page appears. Enter the remote server path and password to access the server. Click Upload. The details are exported to the remote server.
The following sections provide examples and commands (CLI) of TLS/SSL decryption. Refer to the following:
| Example 1: TLS/SSL Decryption with a Regular Map |
| Example 2: TLS/SSL Decryption with De-duplication |
| Other Usage Examples |
In Example 1, a regular map is configured to use with the TLS/SSL decryption GigaSMART operation.
|
Step |
Description |
Command |
|||
|
Upload a key and create a service. Refer to Working with Keys and Services on page 609. |
(config) # apps ssl key alias key1 download type private-key url https://keyserver.domain.com/path/keyfile.pem (config) # apps ssl service alias service1 server-ip 192.168.1.1 server-port 443 |
|||
|
Configure a GigaSMART group.. |
(config) # gsgroup alias gsgrp1 port-list 1/1/e1 |
|||
|
Specify the GigaSMART group alias. |
(config) # gsparams gsgroup gsgrp1 |
|||
|
Specify a failover action. |
(config gsparams gsgroup gsgrp1) # ssl-decrypt decrypt-fail-action drop |
|||
|
Configure session timeouts, in seconds. |
(config gsparams gsgroup gsgrp1) # ssl-decrypt pending-session-timeout 60 (config gsparams gsgroup gsgrp1) # ssl-decrypt session-timeout 300 (config gsparams gsgroup gsgrp1) # ssl-decrypt tcp-syn-timeout 20 |
|||
|
Configure cache timeouts, in seconds. |
(config gsparams gsgroup gsgrp1) # ssl-decrypt key-cache-timeout 9000 (config gsparams gsgroup gsgrp1) # ssl-decrypt ticket-cache-timeout 9000 |
|||
|
Configure a key/service mapping that maps how a key is assigned to an IP address of a server. |
(config gsparams gsgroup gsgrp1) # ssl-decrypt key-map add service service1 key key1 |
|||
|
Enable TLS/SSL decryption. |
(config gsparams gsgroup gsgrp1) # ssl-decrypt enable |
|||
|
Exit the GigaSMART group configuration mode. |
(config gsparams gsgroup gsgrp1) # exit (config) # |
|||
|
Configure a GigaSMART operation for TLS/SSL decryption. |
(config) # gsop alias gdssl1 ssl-decrypt in-port any out-port auto port-list gsgrp1 |
In the previous step, gdssl1 is the alias for a GigaSMART operation, in-port specifies the destination port on which to listen, out-port specifies the destination port on which to send decrypted traffic, and port-list is set to the GigaSMART group alias previously configured. The in-port and out-port arguments can also be a port number between 1 and 65535.
Next, configure a traffic map, as follows:
|
Step |
Description |
Command |
|||
|
Specify a map alias (m1) and specify the map type and subtype. |
(config) # map alias m1 (config map alias m1) # type regular byRule |
|||
|
Specify the GigaSMART operation alias (gdssl1) as part of the map. This applies the associated GigaSMART functionality to packets matching a rule in the map. |
(config map alias m1) # use gsop gdssl1 |
|||
|
Specify a map rule. |
(config map alias m1) # rule add pass ipver 4 |
|||
|
Specify the destination for packets matching this map. |
(config map alias m1) # to 1/1/g2 |
|||
|
Specify the source port(s) for this map. |
(config map alias m1) # from 1/1/g1 |
|||
|
Exit the map prefix mode. |
(config map alias m1) # exit (config) # |
|||
|
Display the configuration. |
(config) # show gsop (config) # show map (config) # show gsparams |
In Example 2, the configuration steps are the same except when you configure a GigaSMART operation you send the decrypted traffic to de-duplication for additional filtering, as follows:
(config) # gsop alias gdssl1 ssl-decrypt in-port any out-port auto dedup set port-list gsgrp1
Two typical usage examples are as follows:
| Use map rules to filter on the IP address of the server and send everything to GigaSMART. Configure a GigaSMART operation to listen on the in-port used by the server. The GigaSMART will drop other traffic. |
| Use map rules to filter on the IP address of the server and in-port and send specific port traffic to the GigaSMART. Configure a GigaSMART operation to listen on in-port any. |
 - The key certificate is attached to a passive TLS/SSL service and the service is part of the passive TLS/SSL GSOP, which is used in a traffic map. This will also indicate a certificate which is being used as a signing CA in outbound deployment .
- The key certificate is attached to a passive TLS/SSL service and the service is part of the passive TLS/SSL GSOP, which is used in a traffic map. This will also indicate a certificate which is being used as a signing CA in outbound deployment . - The key certificate is not actively participating in any traffic flow.
- The key certificate is not actively participating in any traffic flow. - The key certificate has expired .
- The key certificate has expired .


