Configure Thales-Luna HSM for TLS/SSL Decryption
This section describes the configuration and use of Thales-Luna HSM for TLS/SSL decryption.
Prerequsites
|
■
|
From the Thales Luna HSM administrator: |
|
o
|
HSM server IP address and port, and a valid partition label and partition password for the Luna partition you will use. |
|
o
|
The private keys’ key labels in the Luna partition (for example, for primary and secondary signing). With Luna, the private key remains in the HSM; you reference it by its unique label/handle during configuration. |
|
o
|
The corresponding server certificate(s) for those key labels, and any required CA certificate(s) for trust. |
|
■
|
A Keychain password must be configured on the device before installing certificates and keys in the keystore. |
|
■
|
A static IP address to assign to the GigaSMART engine for HSM communication; static IP is recommended. When Luna HSM is selected, IP address configuration details must be entered for the Inline SSL application. |
Access Flexible Inline Canvas
|
1.
|
Go to  > Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas. > Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas. |
|
2.
|
In the displayed Flexible Inline Canvas, select the device where you want to configure the TLS/SSL decryption. |
Configure Inline Network
|
1.
|
On the left pane, click the ‘+’ icon next to Inline Network option to create a new entry. |
|
2.
|
Enter a name and description for the inline network in the Alias and Description fields. Then, click Port Editor. |
|
3.
|
In the Alias and Description fields, enter a name and description for the inline network. |
|
4.
|
Click Port Editor. In the Quick Port Editor, scroll down to the inline network ports that you want to configure. Select Enable to administratively enable inline network ports, and click OK to apply the changes. |
|
5.
|
From the Port A and Port B drop-down lists, select the ports that you want to configure as the inline network pair. |
|
6.
|
From the Traffic Path drop-down list, select To Inline Tool. |
|
o
|
To Inline Tool—All traffic originating from the inline network is directed to the sequence of inline tools and inline tool groups and is guided through the inline tools and inline tool groups according to the current inline tool and inline tool group status.
|
|
7.
|
Click OK. You have successfully created an Inline Network. |
To explore additional options during configuration, refer to Inline Network Ports and Inline Network.
Configure Inline Tool
|
1.
|
On the left pane, click the ‘+’ icon next to the Inline Tool option to create a new inline tool. |
|
2.
|
In the Properties pane, in the Alias and Description fields, enter a name and description for the inline tool. |
|
3.
|
From the Type drop-down list, select one of the following options: |
|
o
|
External- To configure a third-party tool. |
|
o
|
GigaVUE Node- To configure a GigaVUE node as a tool. |
|
4.
|
Click Port Editor. In the Quick Port Editor, scroll down to the inline tool ports that you want to configure. Select Enable to administratively enable the inline tool ports, and then click OK to apply the changes. |
|
5.
|
From the Port A and Port B drop-down lists, select the inline tool ports according to the direction the inline tool expects traffic from the network. |
|
6.
|
Verify that the Enabled check box is selected. |
|
7.
|
Click OK. You have successfully created an Inline Network. |
To explore additional options during configuration, refer to Inline Tool Ports and Inline Tools.
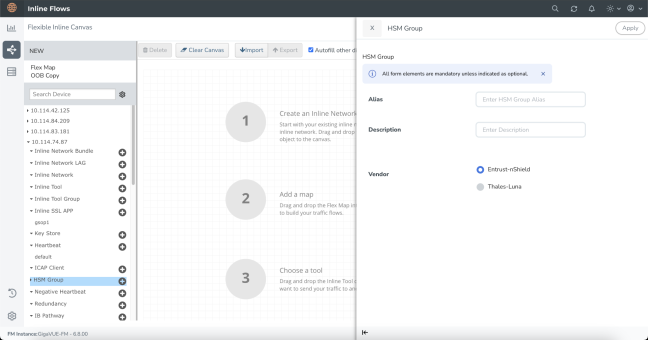
Create HSM Group
To configure HSM Group:
|
1.
|
Go to  > Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas. > Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas. |
|
2.
|
In the displayed Flexible Inline Canvas, select the device where you want to configure the HSM Group. |
|
3.
|
Click the ‘+’ icon next to the HSM Group to create a new entry. |
|
4.
|
Enter a name and description for the HSM Group in the Alias and Description fields. |
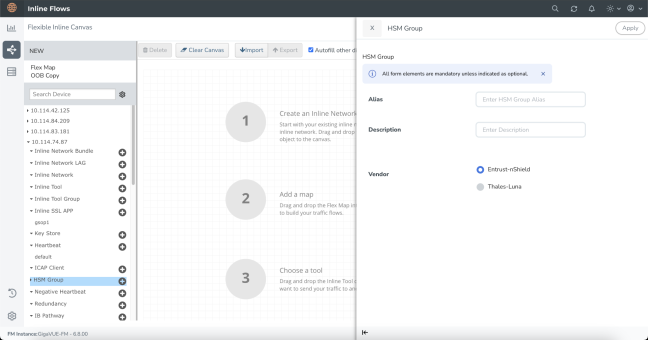
|
5.
|
Select the required vendor type from the available options —Entrust-nShield or Thales-Luna—to create the corresponding HSM Group. |
Note: For Thales-Luna Network HSM, you can create a maximum of 16 HSM units per device.
|
6.
|
Click Apply to save the configurations. All individual HSM units you create will be listed under the configured HSM Group. |
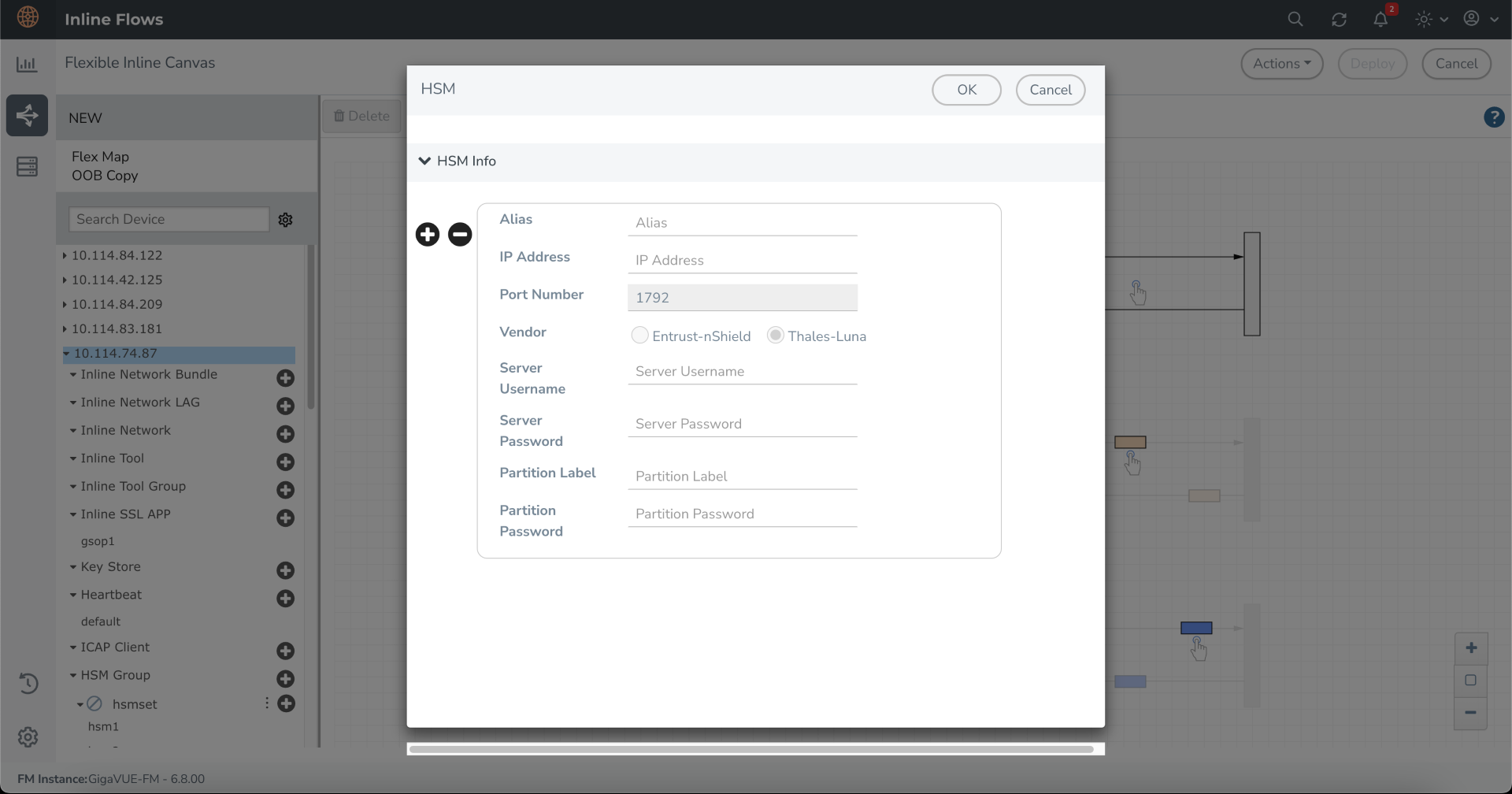
Add Thales -Luna HSM Appliance to the HSM Group
To add your vendor type as Thales-Luna to your configured HSM Group follow the below steps:
|
1.
|
In the Flexible Inline Canvas, select the device for which the HSM Group is configured. |
|
2.
|
Click the expand menu on the configured HSM Group. |
|
3.
|
Click the ‘+’ icon next to the configured Thales-Luna HSM to proceed. |
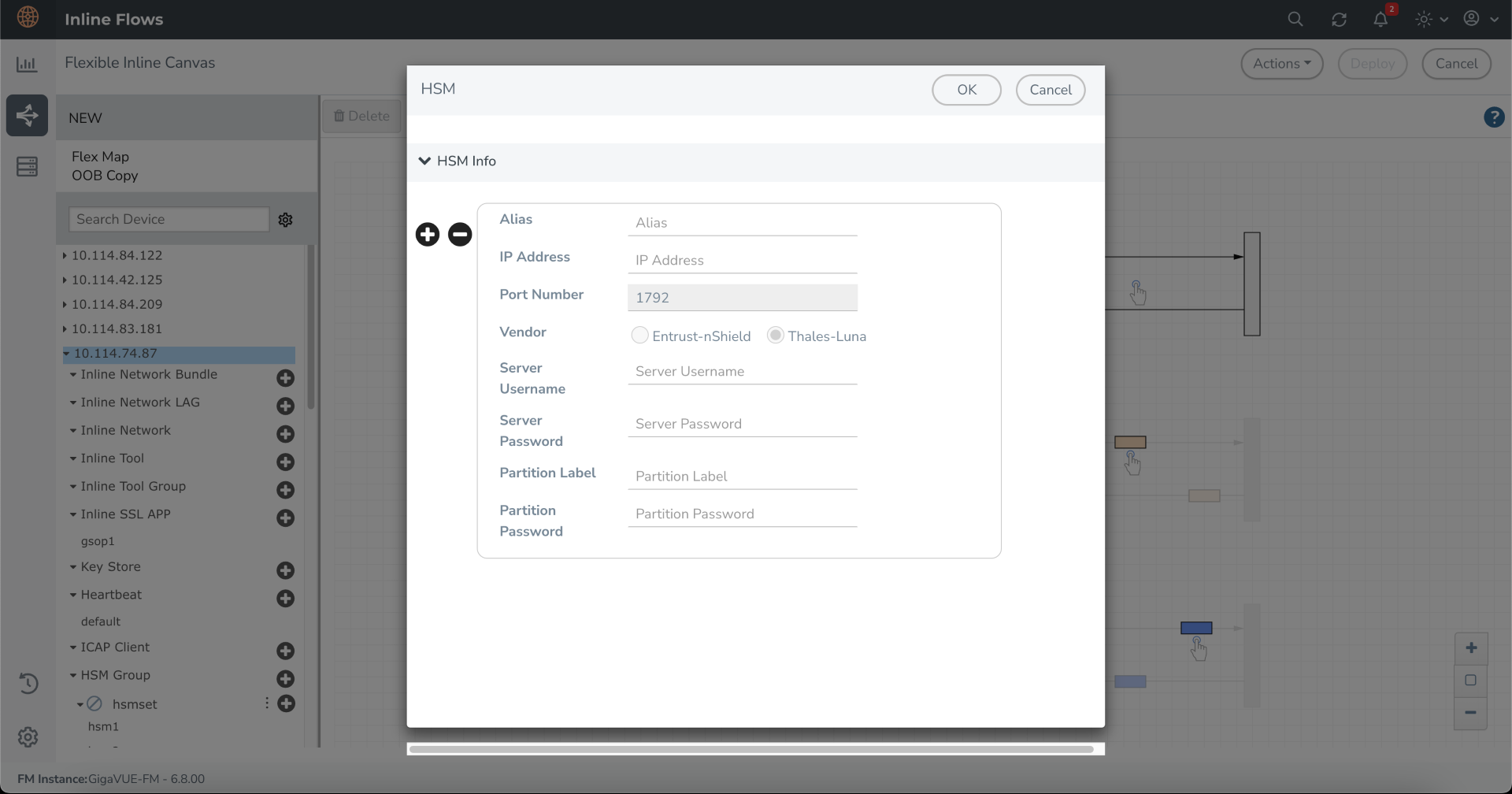
|
4.
|
In the HSM pop-up that appears, enter a name for the HSM appliance in the Alias field. |
|
5.
|
Enter the IP address of the HSM server and Port Number. |
Notes:
- The default port number for Thales- Luna HSM is 1792.
- It is preferable to use a static IP address to prevent the Thales Luna registration from expiring.
|
6.
|
By default, Thales-Luna is selected and Entrust nShield is disabled in the Vendor type when configuring Thales-Luna. |
|
7.
|
Enter the valid username and password in the Server Username and Server Password fields. |
|
8.
|
Enter the valid details in the Partition Label and Partition Password fields. |
Note: When adding multiple HSM appliances, make sure to keep the Partition Password same for all the partitions.
|
9.
|
Click OK to save the configuration. |
Notes
For Thales-Luna configuration, if the operational status of the HSM Group shows 'Registration pending', follow the below steps to register the HSM client (GigaSMART engine) with the HSM server:
|
1.
|
Register the HSM Client (GigaSMART engine’s IP address) on the HSM server. |
Create an Inline SSL APP and Attach the HSM Group
|
1.
|
On the left pane, click the ‘+’ icon next to the Inline SSL APP option. |
|
2.
|
Enter a name for the Inline SSL APP and select the required GigaSMART engines. |
|
3.
|
From the HSM Group drop-down list, select the configured hsm-luna Group alias. |
|
4.
|
Under Deployment Type, set up Key chain Password: |
|
a.
|
Click Keychain Password, and then choose either Add or Reset. |
|
b.
|
If you choose to reset the Keychain Password, enter a password that is 8 to 30 characters long and contains at least one numerical character, one uppercase character, one lowercase character, and one special character. |
|
c.
|
Select the Auto Login check box to enable GigaVUE-FM to unlock the keystore when the device reboots. |
|
d.
|
Click OK to save the Key chain Password. |
|
5.
|
Configure Keys and Certificates. A key in an inbound deployment can be selected only for decryption or for re-signing and re-encryption in an outbound deployment. |
|
a.
|
Click Add Keys to open the Key page.
|
|
b.
|
In the Key Alias and Description fields, enter a name and description for the SSL key. |
|
c.
|
For Key Type, select either RSA or ECDSA. |
|
d.
|
From the File Type drop-down list, select Luna-HSM. |
|
e.
|
Choose one of the following methods to import the required key token: |
|
o
|
Install from URL—Enter a valid directory path including the file name and enter the password to access the server. |
|
o
|
Install from Local Directory—Browse and select the key handler file from your local directory. |
|
f.
|
Choose one of the following methods to import the corresponding certificate: |
|
o
|
Install from URL—Enter a valid directory path including the file name and enter the password to access the server. |
|
o
|
Install from Local Directory—Browse and select the certificate file from your local directory. |
Note: You can obtain the key token and the corresponding certificate from your HSM administrator.
|
g.
|
Click OK. You have successfully created the Primary key. |
|
h.
|
Repeat steps 1-6 to configure the secondary signing certificate and private key. |
|
6.
|
Thales-Luna HSM configuration is supported in Inbound, Outbound, and Hybrid deployment types. Select the required deployment type. Refer to TLS/SSL Sessions for more details. |
|
o
|
Outbound - Add the configured primary and a secondary signing Certificate Authorities (CA). |
|
o
|
Inbound - Add a new Server Key Mapping. Enter the domain name or IP address of the server, and then select the required Key Pair Alias. |
|
o
|
Hybrid - Add a new Server Key Mapping, and a primary and a secondary signing CA. |
|
7.
|
Select Outbound as your deployment type and add the configured primary and a secondary signing Certificate Authorities (CA). |
|
8.
|
Under Configurations, for Default Action select one of the following options: |
|
o
|
Decrypt—Decrypt all the traffic that is guided into the Inline SSL APP. |
|
o
|
No Decrypt—Do not decrypt the traffic that is guided into the Inline SSL APP. |
|
9.
|
For URL Cache Miss Action, select one of the following options |
|
o
|
Decrypt—Decrypt all the traffic that is guided into the Inline SSL APP. |
|
o
|
No Decrypt—Do not decrypt the traffic that is guided into the Inline SSL APP. |
|
o
|
Defer—Delay the decryption until the Defer Timeout seconds provided. |
|
10.
|
Under Security Expectations, choose to either decrypt or drop the traffic for the following certificates: |
|
o
|
Self-signed certificate |
|
11.
|
Under Network Access, select IP Address as the network access configuration mode. Enter the IP Address, Netmask, Gateway, DNS, MTU, and VLAN. |
Notes:
-
DHCP mode is not supported when configuring Thales-Luna HSM, as IP changes can break connectivity if the new address isn’t registered with the HSM server
-
Ensure that IP address you are using is already registered in the HSM server.
|
12.
|
Under Trust Store, set up Set up the Signing Certificate Authority (CA). |
|
o
|
Click Append and choose one of the following methods: |
|
•
|
Copy and Paste - Directly paste the Trust Store Certificate. |
|
•
|
Install from Local Directory - Browse and select the certificate file from your local directory. |
|
o
|
Click Replace to update the existing certificate with a new one. |
|
13.
|
Click OK. You have successfully created the Inline SSL APP. |
Refer to Inline SSL App—Field References for any additional details when configuring the Inline SSL APP.
Deploy the Inline SSL Solution
|
1.
|
Drag and drop the required inline network or inline network bundle into the flexible inline canvas. |
|
2.
|
Drag and drop the flexible inline map into the canvas. |
|
3.
|
In the Properties pane, click Add Rule, and add Bi-directional as the rule condition. |
|
4.
|
In the rule description, add protocol as TCP. Add the required rules for the inline map, and then click OK to save the configuration. |
|
5.
|
Drag and drop the Inline SSL APP into the canvas. |
|
6.
|
Drag and drop the required inline tools or inline tool group into the canvas. |
Register GigaSMART Engine on Thales Luna HSM Server
After deploying the Gigamon configuration, the Luna HSM administrator must register the GigaSMART engine (client) on the Luna HSM using the GigaSMART IP you configured in Network Access.
If client registration is not completed within the required time window ( 10 minutes), operational status can move to a registration timeout state. Work with your HSM admin to complete registration on the Luna HSM side. Refer to Client Register - Luna Command Reference for more details.
Verify the Solution
|
■
|
Confirm the solution is Deployed on the Flexible Inline Canvas (Physical > Orchestrated Flows > Inline Flows > Configuration Canvas) and the Inline SSL app is present in the canvas. |
|
■
|
Verify HSM group, connectivity, and trust |
|
o
|
InGigaVUE-FM, verify the HSM Group exists and is associated to the target node(s). |
|
o
|
Confirm the Thales Luna HSM appliance/client is registered and reachable; check that the Luna partition/slot assignment is correct and shows a healthy/connected state. |
|
o
|
Ensure you are not mixing HSM vendors on the same device (do not combine Entrust and Thales). |
|
■
|
Confirm that the Inline SSL app is using Thales Luna HSM-backed keys (not local files), the Keychain Password is unlocked, and the keys/certificates load without errors or HSM/keystore alerts so they are available for decryption |
|
o
|
In the Inline SSL App’s keys/certificates area: |
|
•
|
Verify each required key/cert shows Thales Luna HSM as the source (HSM‑backed), not local/PEM/PKCS12. |
|
•
|
Ensure the GigaVUE-FM Keychain Password is unlocked so the app can access the keystore. |
|
o
|
Confirm keys/certs load without errors (no red badges or “key not found/permission denied/keystore locked” messages). |
|
o
|
Check Events/Alerts for any HSM‑related issues (e.g., partition login failures, HSM connectivity, permission errors). There should be no HSM/keystore alerts. |
What to Do Next
After deployment, you can view the the statistics details , refer to View HSM Statistics.
|
|
 > Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas.
> Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas. > Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas.
> Physical > Orchestrated Flows > Inline Flows > Configuration Canvas to create a new Flexible Inline Canvas.