Connect to AWS
After creating a environment create a connection between the AWS and GigaVUE‑FM. Refer to the following step given below for detailed information on how to create a new connection.
Create Connection
To create a new Connection:
- Select Inventory > Resources > Environment.
- On the Environments page, on the Connections tab, click Create.
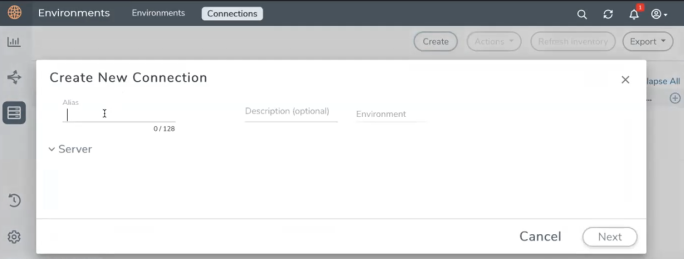
- The Create New Connection dialog box opens. Enter the details as mentioned in the below section.
Note: When creating a connection in the connections page, the corresponding monitoring domain created for internal use in GigaVUE‑FM will not be displayed in the Monitoring Domain list page.
Note: For Application Intelligence solution, you must add the UDP port 2056 for GigaVUE‑FM in your AWS security group.
To connect to AWS, select or enter the following details:
|
Field |
Description |
|||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
Name |
Name used to identify the connection. |
|||||||||
|
Credential |
Select your credentials from the drop-down menu. Refer Create Credentials for detailed information on how to create credentials. |
|||||||||
|
Select Region |
The AWS region for the connection. For example, EU (London). Note: If the region you want to choose is not available in the Region Name list, you can add a custom region. Adding a Custom RegionTo add a custom region:
|
|||||||||
| Select Account | Select the AWS account name/id. | |||||||||
| Select VPCs | Select the VPC | |||||||||
| Traffic Acquisition Method |
Select a Tapping method. The available options are:
Note: For VPC Traffic Mirroring option, additional permissions are required. Refer to the Permissions for details. |
|||||||||
| MTU |
The Maximum Transmission Unit (MTU) is the maximum size of each packet that the tunnel endpoint can carry. Note: The default MTU is 1450. You can edit the MTU value according to your requirements. The valid range is between 1450 to 9000. |
In the AWS Virtual Node Deployment page, select or enter the following details and click Next:
|
Fields |
Description |
|||||||||
|
Centralized VPC |
Alias of the centralized VPC in which the UCT-V Controllers, V Series Proxies and the GigaVUE V Series nodes are launched. |
|||||||||
|
EBS Volume Type |
The Elastic Block Store (EBS) volume that you can attach to the fabric components. The available options are:
|
|||||||||
|
SSH Key Pair |
The SSH key pair for the GigaVUE fabric nodes. |
|||||||||
|
Management Subnet |
The subnet that is used for communication between the controllers and the nodes, as well as to communicate with GigaVUE-FM. This is a required field. |
|||||||||
|
Enable Custom Certificates |
Enable this option to validate the custom certificate during SSL Communication. GigaVUE-FM validates the Custom certificate with the trust store. If the certificate is not available in Trust Store, communication does not happen, and an handshake error occurs. Note: If the certificate expires after the successful deployment of the fabric components, then the fabric components moves to failed state. |
|||||||||
|
Certificate |
Select the custom certificate from the drop-down menu. You can also upload the custom certificate for GigaVUE V Series Nodes, GigaVUE V Series Proxy, and UCT-V Controllers. For more detailed information, refer to Install Custom Certificate. |
|||||||||
|
Security Groups |
The security group created for the GigaVUE fabric nodes. |
Enable the Configure a V Series Proxy toggle button if you wish to deploy V Series nodes using a proxy. In the V Series Proxy section, select or enter the values for the fields as described in the below table.
|
Fields |
Description |
|||||||||
|
Version |
GigaVUE V Series Proxy version. |
|||||||||
|
Instance Type |
Instance type for the GigaVUE V Series Proxy. The recommended minimum instance type is t2.micro. You can review and modify the number of instances for the nitro-based instance types in the Configure AWS Settings page. |
|||||||||
|
Number of Instances |
Number of GigaVUE V Series Proxy to deploy in the monitoring domain. |
|||||||||
|
Set Management Subnet |
Use the toggle button to select a management subnet.
|
|||||||||
|
Set Security Groups |
Toggle option to Yes to set the security group that is created for the GigaVUE V Series Proxy. Refer to Security Group for more details. |
|||||||||
|
IP Address Type |
Select one of the following IP address types:
The elastic IP address does not change when you stop or start the instance. |
|||||||||
|
Additional Subnets |
(Optional) If there are GigaVUE V Series Nodes on subnets that are not IP routable from the management subnet, additional subnets must be specified so that the GigaVUE V Series Proxy can communicate with all the GigaVUE V Series Nodes. Click Add to specify additional subnets, if needed. Also, make sure that you specify a list of security groups for each additional subnet. |
|||||||||
|
Tags |
(Optional) The key name and value that helps to identify the GigaVUE V Series Proxy instances in your AWS environment. |
In the UCT-V Configuration section, select or enter the following details:
|
Fields |
Description |
||||||||||||
|
Controller Version |
The UCT-V Controller version. If there are multiple versions of UCT-Vs deployed in the EC2 instances, then you must configure multiple versions of UCT-V Controllers that matches the version numbers of the UCT-Vs. Note: If there is a version mismatch between UCT-V Controllers and UCT-Vs, GigaVUE-FM cannot detect the agents in the instances. Click Add to add multiple versions of UCT-V Controllers: An older version of UCT-V Controller can be deleted once all the UCT-Vs are upgraded to the latest version. |
||||||||||||
|
Instance Type |
The instance type for the UCT-V Controller. The recommended minimum instance type is nitro-based starting from t2.micro. Note: GigaVUE V Series Node solution does not support non-nitro-based instance types. |
||||||||||||
|
Number of Instances |
The number of UCT-V Controllers to deploy in the monitoring domain. |
||||||||||||
|
Agent Tunnel Type |
The type of tunnel used for sending the traffic from UCT-Vs to GigaVUE V Series nodes. The options are GRE or VXLAN tunnels. If any Windows agents co-exist with Linux agents, VXLAN must be selected. |
||||||||||||
|
Agent Tunnel CA |
The Certificate Authority (CA) that should be used in the UCT-V Controller for connecting the tunnel. |
||||||||||||
|
UCT-V MTU (Maximum Transmission Unit) |
The Maximum Transmission Unit (MTU) is the maximum size of each packet that the tunnel endpoint can carry from the UCT-V to the GigaVUE V Series node.
AWS Platform MTU is 9000
|
||||||||||||
|
IP Address Type |
The IP address type. Select one of the following:
Note: The elastic IP address does not change when you stop or start the instance. |
||||||||||||
|
Additional Subnet(s) |
(Optional) If there are UCT-Vs on subnets that are not IP routable from the management subnet, additional subnets must be specified so that the UCT-V Controller can communicate with all the UCT-Vs. Click Add to specify additional subnets, if needed. Also, make sure that you specify a list of security groups for each additional subnet. |
||||||||||||
|
Tag(s) |
(Optional) The key name and value that helps to identify the UCT-V Controller instances in your AWS environment. For example, you might have UCT-V Controllers deployed in a VPC. To identify the UCT-V Controllers you can provide a name that is easy to identify such as us-west-2-uctv-controllers. To add a tag,
|
In the V Series Node configuration section, select or enter the following:
|
Fields |
Description |
||||||
|
Version |
GigaVUE V Series Node version. |
||||||
|
Instance Type |
The instance type for the GigaVUE V Series Node. The default instance type is nitro-based t3a.xlarge. You can review and modify the number of instances for the nitro-based instance types in the Configure AWS Settings page. |
||||||
|
IP Address Type |
Select one of the following IP address types:
The elastic IP address does not change when you stop or start the instance. |
||||||
|
Min Number of Instances |
The minimum number of GigaVUE V Series Nodes that must be deployed in the monitoring domain. The minimum number of instances must be 1. When 0 is entered, no GigaVUE V Series Node is launched. Note: If the minimum number of instances is set as ‘0’, then the nodes will be launched when a monitoring session is deployed if GigaVUE-FM discovers some targets to monitor. |
||||||
|
Max Number of Instances |
The maximum number of GigaVUE V Series Nodes that can be deployed in the monitoring domain. |
||||||
|
Tunnel MTU |
The Maximum Transmission Unit (MTU) on the outgoing tunnel endpoints of the GigaVUE V Series Node when a monitoring session is deployed. The UCT-V and controller tunnel MTU should be 50 bytes less than the agent's destination interface MTU size. The default value is 9001. |
||||||
|
Data Subnets |
The subnet that receives the mirrored GRE or VXLAN tunnel traffic from the UCT-Vs. Note: Using the Tool Subnet checkbox you can indicate the subnets to be used by theGigaVUE V Series to egress the aggregated/manipulated traffic to the tools. |
Use the following buttons to manage your AWS connections :
|
Button |
Description |
| Create | Use to create new connection. |
| Actions |
Provides the following options:
|
| Refresh Inventory | Use to refresh the entire connections page. |
| Export | Use to export the details from the Connections page into an XLS or a CSV file. |



