Inline TLS/SSL Decryption Deployments
Inline TLS/SSL decryption can be deployed in two main ways – Inbound and Outbound.
Inbound Deployment
In an inbound deployment, the client is on the Internet, and the server is inside the enterprise network. The GigaVUE node is also deployed inside the network, on the server side. To decrypt traffic, the GigaVUE node must have access to the server's private keys. This setup enables Man-in-the-Middle (MitM) decryption. The traffic uses Diffie-Hellman or Perfect Forward Secrecy (PFS) encryption.
Refer to Diagram 1 for an example of inbound inline TLS/SSL decryption deployment.
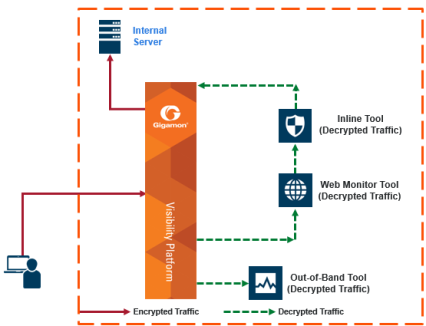
| 1 | Inbound Deployment of Inline TLS/SSL Decryption |
Inbound Deployment with Client Certificate Authentication (mTLS)
In a standard inbound deployment, the GigaVUE node is deployed on the server side and decrypts traffic destined for internal servers using their private keys. With mTLS enabled, the same topology can enforce client certificate authentication at the inline TLS/SSL layer.
In this deployment model:
| The client resides on the Internet or external network. |
| The server and GigaVUE node reside inside the protected enterprise network. |
| The server is configured to require client certificates for selected applications (for example, user‑facing portals or API endpoints). |
| The Inline TLS/SSL application: |
| Validates the server certificate against the server trust store. |
| Validates the client certificate against the client trust store. |
| Applies policy to accept or reject the session based on the outcome of both validations. |
The resulting end‑to‑end connection is still an mTLS session from the client’s perspective, but certificate validation and decryption are offloaded to the Inline TLS/SSL solution, which then forwards clear‑text traffic to inline tools for inspection.
Outbound Deployment
In an outbound deployment, the client is inside the enterprise network, along with the GigaVUE node, which is deployed on the client side. The server is external, located on the Internet. In this case, the GigaVUE node acts as a trusted Man-in-the-Middle (MitM) but does not require access to the server’s private key. It can still inspect TLS/SSL traffic.
Refer to Diagram 2 for an example of outbound inline TLS/SSL decryption deployment.
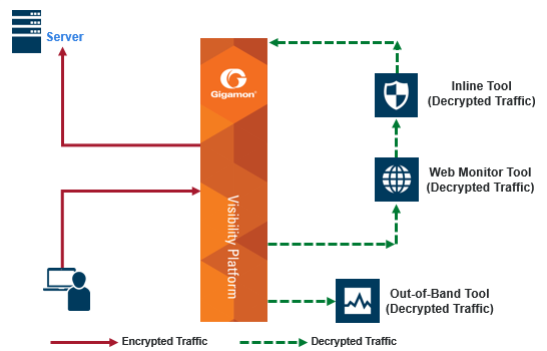
| 2 | Outbound Deployment of Inline TLS/SSL Decryption |



