Configure Flexible Inline Decryption Solution
Refer to the following sections that provide details about the flexible inline decryption solution and instructions on how to configure it:
| About Flexible Inline Decryption Solution |
| Benefits of Flexible Inline Decryption Solution |
| Flexible Inline Decryption Solution—Rules and Notes |
| Configure Flexible Inline Decryption Solution |
About Flexible Inline Decryption Solution
The flexible inline decryption solution combines the flexible inline arrangements feature with the inline decryption solution. It includes the GigaSMART-based packet processing, which is the inline decryption functionality into the flexible inline arrangements framework. In the flexible inline decryption solution, the outer maps guide the inline traffic to GigaSMART for preprocessing. The inner map guides the traffic processed by GigaSMART through a user-defined sequence of inline tools and inline tool groups.
Figure 1 illustrates an example of how the inline decryption functionality is incorporated in the flexible inline arrangements framework to form the flexible inline decryption solution.
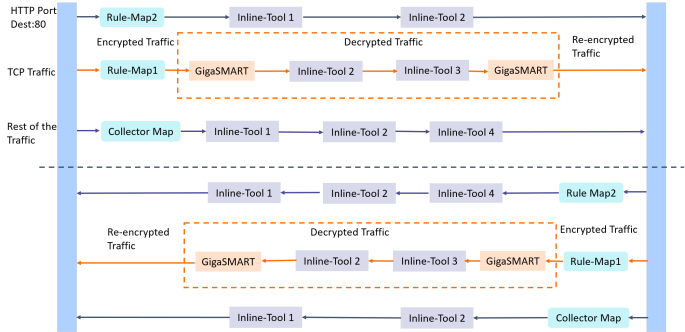
| Figure 53 | Flexible Inline Decryption Solution |
In this example, the HTTP Port Destination:80 traffic is guided through the Flexible inline map, Rule Map2 to the sequence of inline tools, Inline Tool 1 and Inline Tool 2. The TCP traffic is encrypted and guided through Rule Map1 to GigaSMART, where it is decrypted and guided to Inline Tool 2 and Inline Tool 3. The decrypted traffic is guided back to GigaSMART, and then it is re-encrypted and routed to the network. Here, the Rule Map 1 is the outer map, which guides the traffic to GigaSMART for preprocessing. The inner map guides the traffic processed by GigaSMART through a series of inline tools or inline tool groups.
The rest of the traffic is guided through the Collector Map to a series of inline tools, and then to the network.
Figure 2 illustrates the different maps that guide the traffic in the flexible inline decryption solution.
The outer maps are similar to the flexible inline maps but include virtual port alias along with inline tools and inline tool groups as the destination port. The same virtual port alias can be used in multiple outer maps.
Depending on the flexible inline decryption solution that you create, there may be two types of inner maps:
| Inner Proxy Maps, which guides the traffic from GigaSMART to the inline tools or inline tool groups. |
| Inner Non-proxy Maps or Network-end Maps, which guide the traffic that is bypassed from GigaSMART to the inline tools or inline tool groups. |
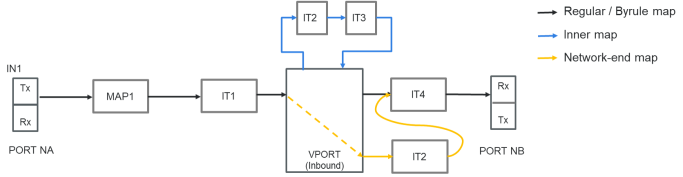
| Figure 54 | Flexible Inline Decryption Maps |
Benefits of Flexible Inline Decryption Solution
The flexible inline decryption solution incorporates the inline decryption with the flexible inline arrangement and offers the following benefits:
| Enables you to perform the inline decryption configuration, required map deployments, and flexible inline flow configurations, all in one canvas. |
| Shares the same inline tool or inline tool group across multiple inline network links and across multiple inline maps. Refer to Figure 3 Flexible Inline SSL APP—Deployed. |
| Allows you to tap OOB copies of decrypted traffic from GigaSMART, either before or after the inspection of security tools. Refer to Figure 3 Flexible Inline SSL APP—Deployed. |
| Allows you to selectively decrypt and guide traffic to the attached inline tools or inline tool groups. |
Flexible Inline Decryption Solution—Rules and Notes
Keep in mind the following rules and notes when working with flexible inline decryption solution:
| When you want to migrate from the inline decryption to the flexible inline decryption solution, |
| ensure that you delete all the inline decryption virtual ports, GigaSMART, and maps configurations, and then reconfigure them using the flexible inline canvas. However, if there are OOB maps from the inline network ports, before you delete the OOB maps, ensure that the Traffic Path for the inline network is not set to ‘Bypass’. |
| It is recommended to delete the OOB map from vPort before deleting other maps. If the OOB map from the vPort is not deleted while deleting all the inline SSL maps, then GigaVUE‑FM throws an error on first time. You need to click Delete All again to delete all the maps. |
| Modifying the VLAN settings on an out-of-band map is not allowed if another out-of-band map has the same port as destination. |
| When there is a multiple tool failover across the inner and outer maps; and if any of the tool comes up, the traffic in the inline network does not flow as expected. |
| If you want to switchover from the flexible inline decryption solution to the inline decryption solution, you must delete the flexible inline SSL APP, and then reconfigure the ports, GigaSMART, and maps using the inline decryption workflow. |
| When you configure the flexible inline decryption solution using GigaVUE-FM, the keychain password will be unlocked automatically when the device participating in the solution reboots. |
| If an inline SSL profile is used across multiple map configurations with different inline network pairs, the tool set used across the maps is also the same. Consider the following example: |
Flexible Inline Map 1 with inline network pair 1 uses inline SSL Profile 1 with tools A and B.
Flexible Inline Map 2 with inline network pair 2 also uses inline SSL Profile 1. This map also has tools A and B (filled in automatically). You cannot configure this as A or C or A, C.
Configure Flexible Inline Decryption Solution
Following are the prerequisites that you must complete before you configure the flexible inline decryption solution:
| Configure the required inline networks or inline network bundle. Refer to Configure Inline Network Ports and Inline Network or Configure Inline Network Bundle. |
| Configure the required inline tools. Refer to Configure Inline Tool Ports and Inline Tools. |
| Configure the required inline tool group. Refer to Configure Inline Tool Group. |
| Ensure that there are no inline decryption configurations such as inline decryption policy, inline decryption virtual port, GigaSMART group, GigaSMART operations, or inline decryption map configured on the device. |
To configure a flexible inline decryption solution:
| 1. | On the left navigation pane, go to Physical > Orchestrated Flows > Inline Flows, and then click Configuration Canvas to create a new Flexible Inline Canvas. |
| 2. | In the Flexible Inline Canvas that appears, select the required device for which you want to configure the flexible inline decryption solution. |
| 3. | Click the ‘+’ icon next to the Inline SSL APP option to create a new flexible inline decryption solution. |
| 4. | In the Inline SSL APP page that appears, enter a name for the Inline SSL APP, and then complete the required fields. Refer Inline SSL App—Field References for details. |
| 5. | Click OK to save the configurations. |
| 6. | Drag and drop the required inline network or inline network bundle in to the flexible inline canvas. |
| 7. | Drag and drop the flexible inline map into the canvas. |
| 8. | In the Properties pane, in the Alias and Description fields, enter the name and description of the inline map. |
| 9. | Enter the Tool Side VLAN Tag for the inline network for which you are configuring the map. |
| 10. | Add the required rules for the inline map, and then click OK to save the configuration. |
| 11. | Drag and drop the Inline SSL APP into the canvas. |
| 12. | Drag and drop the required inline tools or inline tool group into the canvas. |
| 13. | Drag and drop the OOB Copy into the canvas, if required. |
| 14. | Click Deploy. |
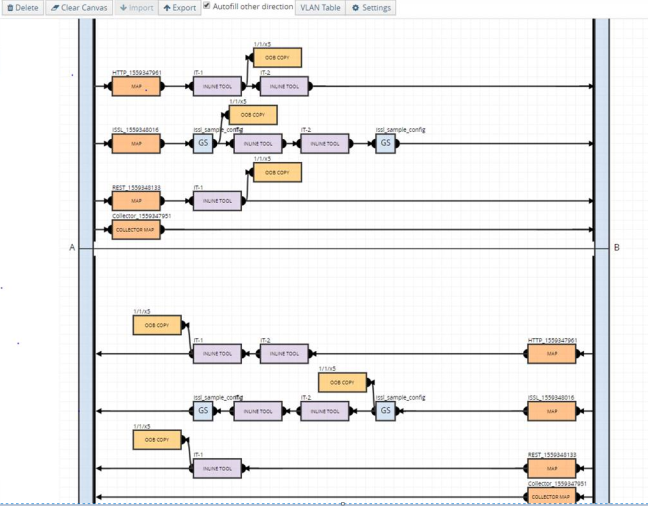
| Figure 55 | Flexible Inline SSL APP—Deployed |
Inline SSL App—Field References
The following table lists and describes the attributes that define the flexible inline decryption solution.
|
Field |
Description |
||||||||||||||||||
|
Alias |
Enter a unique name for the flexible inline SSL APP. |
||||||||||||||||||
|
GS engines |
Select the required GigaSMART engines. |
||||||||||||||||||
|
SSL Monitor Mode |
Select an SSL Monitor Mode from one of the following options:
Refer to Inline SSL Monitor Mode for details. |
||||||||||||||||||
|
Keychain Password |
The keychain password must be configured before installing certificates and keys. Refer to For Inbound and Outbound Inline-SSL deployments, the keychain password must be configured before installing the certificates and private keys into the keystore. for details. To add or reset the Keychain Password:
|
||||||||||||||||||
|
Add new keys |
To configure a certificate-key pair:
|
||||||||||||||||||
|
Deployment Type |
Select one of the following deployment types:
Refer to SSL Keys and Certificates and Generate and Add a Certificate to Key Store for details. |
||||||||||||||||||
|
Configurations |
|||||||||||||||||||
|
Default Action |
Select one of the following option:
|
||||||||||||||||||
|
URL Cache Miss Action |
Select one of the following options:
|
||||||||||||||||||
|
Tool Fail Action |
The failover action taken in response to a failure of an inline tool. Select one of the following options:
|
||||||||||||||||||
|
Tool Bypass |
Select the required options:
|
||||||||||||||||||
|
High Availability |
Select the check box to detect the link switchover by upstream device that is in active or standby mode. Note: Do not select this check box if the inline network links are in active state. Refer to High Availability Active Standby for details. |
||||||||||||||||||
|
Network Group Multiple Entry |
Select this check box to allow the traffic from different inline network to reenter GigaSMART. Refer to Inline Network Group Multiple Entry for details. |
||||||||||||||||||
|
Tool Early Engage |
Select this check box to allow the inline tools to change the MAC address or VLAN IDs. When a connection request is received from the client, GigaSMART establishes the connection with the inline tool first, before connecting with the server. This helps the inline tools to modify the MAC address or VLAN IDs when sending the traffic back to the server. Refer to Tool Early Engage for additional information and limitations. |
||||||||||||||||||
|
StartTLS Port |
Enter the required SSL/TLS ports. Refer to StartTLS and HTTP CONNECT for details. |
||||||||||||||||||
|
Traffic Path |
|||||||||||||||||||
|
Tool Side VLAN Tag |
Enter the required tool side VLAN tag for the inline network. |
||||||||||||||||||
|
Traffic Path |
Select one of the following options:
Note: You can select the Monitoring option only if you have set the SSL Monitor Mode to either Enable or Inline.
|
||||||||||||||||||
|
Inline Failover Action |
Select one of the following options:
|
||||||||||||||||||
|
Security Exceptions |
You can choose to either decrypt or drop the traffic for the following certificates:
You can also choose to configure the security exceptions for certificate revocation validation based on OCSP or CRL on inline decryption profile. Select one of the following options:
Refer to Certificate Revocation List (CRL), Online Certificate Status Protocol (OCSP), CRL and OCSP, and Checking Certificate Revocation Status for details. |
||||||||||||||||||
|
No-decrypt list/Decrypt list |
Select the following check boxes:
Refer to No-decrypt Listing Policy and Decrypt Listing Policy for details. |
||||||||||||||||||
|
Policy Rules |
Add the required policy rules for the inline decryption profile. |
||||||||||||||||||
|
Network Access |
Network access configuration is used to get URL categorization updates. Refer to URL Categorization for details. To configure the network access for the GigaSMART engine ports:
Note: The Eth3 option is available only for GigaVUE‑HC3 devices.
|
||||||||||||||||||
|
Decryption Port Mapping |
The TCP destination port for decrypted traffic sent to inline tools can be configured as part of the inline decryption profile. Configure the required Priority 1 map, which is user configurable and Priority 2 map, which is the default out port. Refer to Inline SSL Decryption Port Map for details. |
||||||||||||||||||
|
Trust Store |
The trust store contains a trusted certificate authority (CA) for server validation. You can choose to either append or replace the trust store. Refer to Trust Store for details. |
||||||||||||||||||
|
TCP Settings |
Configure the required TCP settings as follows:
|
||||||||||||||||||
|
Split-Proxy Settings |
|||||||||||||||||||
|
Split-Proxy |
Select the check box to enable the split proxy settings for the inline decryption solution. The TLS connection between the server and client is divided into two independent connections and the security parameters are kept separate. |
||||||||||||||||||
|
Non-PFS Ciphers (Server) |
Select the check box to enable the non-PFS ciphers settings for the inline decryption solution that has the split proxy settings enabled. This setting is to indirectly force the server to use protocols that are lower than TLS1.3 with non-PFS ciphers. This means that the ciphers with DHE/ECDHE key-exchange will not be used on the server side. |
||||||||||||||||||
|
Miscellaneous (Global Settings) |
|||||||||||||||||||
|
SSL/TLS Version |
Select the minimum and maximum SSL/TLS version. |
||||||||||||||||||
|
Connection Reset Action |
Select one of the following options for the minimum SSL/TLS version:
Select one of the following options for the maximum SSL/TLS version:
|
||||||||||||||||||
|
Caching persistence |
Select this check box to allow the information to be saved on the GigaVUE node in the control card’s persistent storage so that it can be retrieved in case of reboots. Refer to Cache Persistence for details. |
||||||||||||||||||
Support for unattended restart of SSL decryption in managed nodes
The keychain is an encrypted database of certificates and private keys. On individual nodes, the keychain is stored in flash memory until reboot. The user needs to enter keychain password to access keychain. The keychain password is cached in the RAM of the control plane processor to allow decryption of the keychain file, but the keychain password is not cached across reboots. The SSL/TLS processing is not possible without the keychain password.
The keychain password is stored in GigaVUE‑FM to automatically unlock the keychain during reboots and processing the SSL decryption without any intervention. The keychain password is stored in an encrypted database for key protection and risk management. Enable the Auto Login option when you set up or reset the keychain password to automatically unlock the keychain during reboots.



