Create Roles
This section describes the steps for creating roles and assigning user(s) to those roles.
GigaVUE‑FM has the following default roles:
| fm_super_admin — Allows a user to do everything in Fabric Manager, including adding or modifying users and configuring all AAA settings in the RADIUS, TACACS+, and LDAP tabs. Can change password for all users. |
| fm_admin — Allows a user to do everything in Fabric Manager except add or modify users and change AAA settings. Can only change own password. |
| fm_user — Allows a user to view everything in Fabric Manager, including AAA settings, but cannot make any changes. |
Starting in software version 5.7, you can create custom user roles in addition to the default user roles in GigaVUE‑FM. Access control for the default roles and the custom roles is based on the categories defined in GigaVUE‑FM. These categories provide the ability to limit user access to a set of managed inventories such as ports, maps, cluster, forward list and so on.
Refer to the following table for the various categories and the associated resources:
Note: Hover your mouse over the resource categories in the Roles page to view the description of the resources in detail.
|
Category |
Associated Resources |
|||||||||||||||||||||||||||
|
All |
Manages all resources
|
|||||||||||||||||||||||||||
|
Infrastructure Management |
Manages resources such as devices, cards, ports and cloud resources. You can add or delete a device in GigaVUE‑FM, enable or disable cards, modify port parameters, set leaf-spine topology. The following resources belong to this category:
Note: Cloud APIs are also RBAC enabled.
|
|||||||||||||||||||||||||||
|
Traffic Control Management |
Manages inline resources, flow maps, GigaSMART applications, second level maps, map chains, map groups. The following resources belong to this category:
Note: Cloud APIs are also RBAC enabled. |
|||||||||||||||||||||||||||
|
FM Security Management |
Ensures secure GigaVUE‑FM environment. Users in this category can manage user and roles, AAA services and other security operations. |
|||||||||||||||||||||||||||
|
System Management |
Controls system administration activities of GigaVUE‑FM. User in this category are allowed to perform operations such as backup/restore of GigaVUE‑FM and devices, and upgrade of GigaVUE‑FM. The following GigaVUE‑FM resources belong to this category:
|
|||||||||||||||||||||||||||
|
Forward list/CUPS Management |
Manages the forward list configuration. The following resources belong to this category:
|
|||||||||||||||||||||||||||
|
Device Certificate Management |
Manages device certificates. |
|||||||||||||||||||||||||||
|
Other Resource Management |
Manages virtual and cloud resources |
You can associate the custom user roles either to a single category or to a combination of categories based on which the users will have access to the resources. For example, you can create a ‘Physical Devices Technician’ role such that the user associated with this role can only access the resources that are part of the Physical Device Infrastructure Management.
Note: A user with fm_admin role has both read and write access to all of the categories, but has read only access to the FM Security Management category.
To create a role:
| 1. |
On the left navigation pane, click |
| 2. | Click Create. In the Wizard that appears, perform the following steps. Click Continue to progress forward and click Back to navigate backward and change details. |
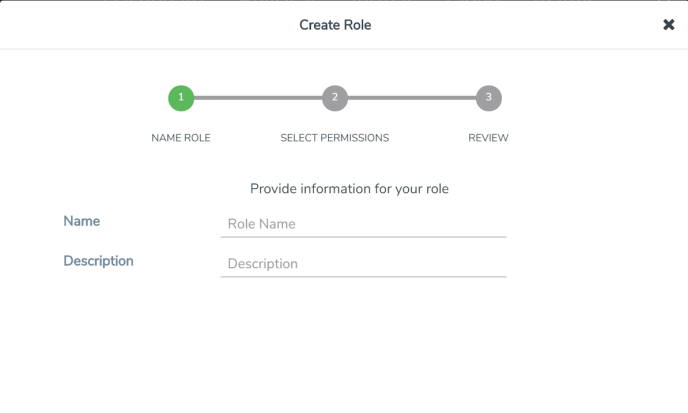
| Figure 15 | Create Roles |
| a. | In the Name Role tab enter the following: |
| Name: Name of the role. |
| Description: Description for the role. |
| b. | In the Select Permissions tab: |
| Select the required resources. Hover your mouse over the resource category to get a glimpse of the resource. |
| Select the required read and write permissions for the resources selected. |
| c. | In the Review tab, review the role created. Click Save to create the role. |
The new role is added to the summary list view.
The following tables describes how access control is applied to a user who has the required role to access the resources based on:
| RBAC settings in the device |
| RBAC mode selected in GigaVUE‑FM |
| RBAC Settings on the Managed Devices | RBAC Mode in GigaVUE‑FM | Access control |
|
Allows user to access its resource
|
Device RBAC |
Allow user to access GigaVUE‑FM resources |
|
Allow user to access managed device resources
|
||
|
GigaVUE‑FM RBAC (node credentials has admin privileges) |
Allow user to access GigaVUE‑FM resources |
|
|
Allow user to access managed device resources
|
||
|
Disallows user to access its resource |
Device RBAC |
Allow user to access GigaVUE‑FM resources |
|
Disallow user to access managed device resources
|
||
|
GigaVUE‑FM RBAC (Node credential has admin privileges) |
Allow user to access GigaVUE‑FM resources |
|
|
Allow user to access managed device resources |
Note: Refer to the following notes:
| For users who do not have the necessary role to access the resources, the access controls mentioned above are disallowed irrespective of the RBAC settings on the managed devices and the RBAC mode in GigaVUE‑FM. |
| For users authenticated using the remote authentication servers such as LDAP or TACACS+, user groups will be assigned to the user based on the mapped-user group configuration. Refer to Authentication for more details about role-mapping in LDAP and TACACS+ based authentication. |



